Search
Now showing items 21-30 of 34
Discrete event simulation of a multi robot pick and place system for reinforcement learning research
(Technological University of the Shannon Midlands Midwest, 2022-01)
This poster described a implementation of simulation environment for a Pick and
Place conveyer belt for multi robot system based on the Gym library to be used to
train Reinforcement Learning agents - see figure below. ...
Blockchain for decentralized multi-drone to combat COVID-19
(Wiley, 2021-03-17)
Currently, drones represent a promising technology for combating Coronavirus disease 2019 (COVID-19) due to the transport of goods, medical supplies to a given target location in the quarantine areas experiencing an epidemic ...
Applying process mining to improve microservices cyber security situational awareness.
(Athlone Institute of Technology, 2020-06)
Cyber Security Incident Response Teams (CSIRTs) for enterprise networks are often overwhelmed by newer, more sophisticated forms of cyber attack. Improved cyber security techniques are in high demand. At present, microservices ...
An Evaluation of Lower Facial Micro Expressions as an Implicit QoE Metric for an Augmented Reality Procedure Assistance Application.
(2020)
Augmented reality (AR) has been identified as a key technology to enhance worker utility in the context of increasing automation of repeatable procedures. AR can achieve this by assisting the user in performing complex and ...
SoK: context and risk aware access control for zero trust systems
(Wiley/Hindawi, 2022-06-30)
Evolving computing technologies such as cloud, edge computing, and the Internet of )ings (IoT) are creating a more complex,
dispersed, and dynamic enterprise operational environment. New security enterprise architectures ...
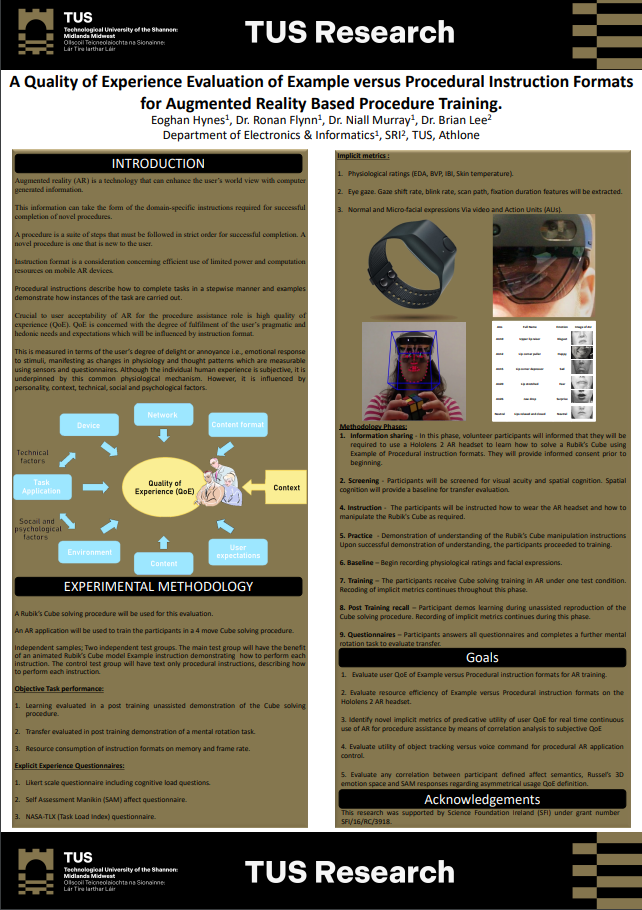
A quality of experience evaluation of example versus procedural instruction formats for augmented reality based procedure training
(TUS Midlands Midwest, 2022)
Augmented reality (AR) is a technology that can enhance the user’s world view with computer
generated information.
This information can take the form of the domain-specific instructions required for successful
completion ...
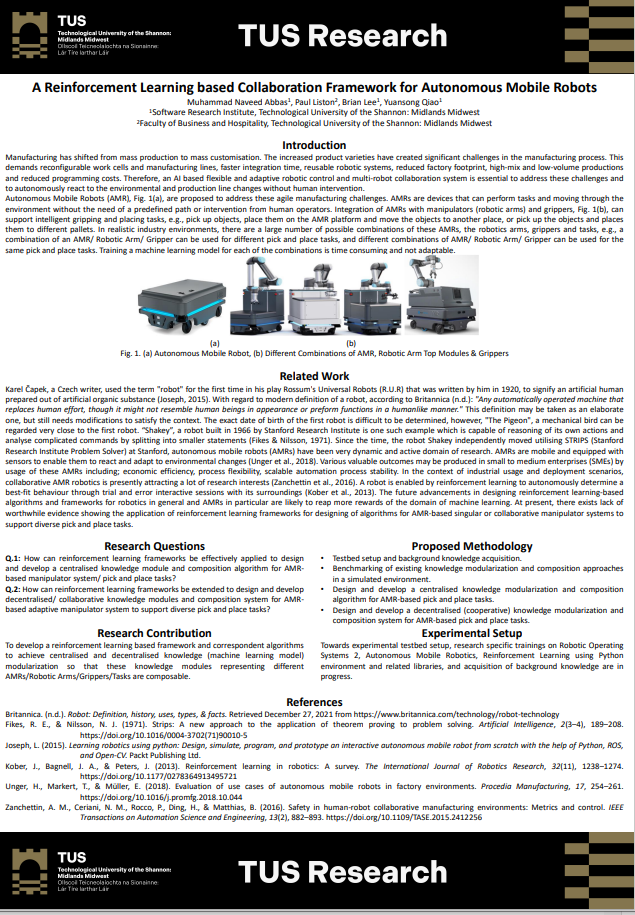
A reinforcement learning based collaboration framework for autonomous mobile robots
(Technological University of the Shannon Midlands Midwest, 2022)
Manufacturing has shifted from mass production to mass customisation. The increased product varieties have created significant challenges in the manufacturing process. This
demands reconfigurable work cells and manufacturing ...
Anomalous distributed traffic: detecting cyber security attacks amongst microservices using graph convolutional networks
(Elsevier, 2022-04-22)
Currently, microservices are trending as the most popular software application design architecture. Software organisations are also being targeted by more cyber-attacks every day and newer security measures are in high ...
A study of network intrusion detection systems using artificial intelligence/machine learning
(MDPI, 2022-11-18)
The rapid growth of the Internet and communications has resulted in a huge increase in
transmitted data. These data are coveted by attackers and they continuously create novel attacks to
steal or corrupt these data. The ...
Pixdoor: a pixel-space backdoor attack on deep learning models
(IEEE, 2021-08-23)
Deep learning algorithms outperform the machine
learning techniques in various fields and are widely deployed
for recognition and classification tasks. However, recent research
focuses on exploring these deep learning ...