Browsing Technological University of the Shannon: Midlands Midwest by Author "Lee, Brian"
Now showing items 1-20 of 69
-
Access control policy enforcement for zero-trust-networking.
Vanickis, Roman; Jacob, Paul; Dehghanzadeh, Sohelia; Lee, Brian (IEEE, 2018-06)The evolution of the enterprise computing landscape towards emerging trends such as fog/edge computing and the Industrial Internet of Things (IIoT) are leading to a change of approach to securing computer networks to deal ... -
Age and gender influences on perceived olfactory and visual media synchronization.
Murray, Niall; Qiao, Yuansong; Karunakar, A. K.; Lee, Brian; Muntean, Gabriel-Miro (IEEE, 2013)Lately, significant efforts have being put into proposing various solutions for increasing multimedia viewers’ perceived quality levels. One innovative avenue is to enhance users’ quality of experience (QoE) by extending ... -
Anomalous distributed traffic: detecting cyber security attacks amongst microservices using graph convolutional networks
Jacob, Stephen; Qiao, Yuansong; Ye, Yuhang; Lee, Brian (Elsevier, 2022-04-22)Currently, microservices are trending as the most popular software application design architecture. Software organisations are also being targeted by more cyber-attacks every day and newer security measures are in high ... -
Anomaly detection in cyber security
Chawla, Ashima; Jacob, Paul; Lee, Brian; Fallon, Sheila (Athlone Institute of Technology, 2020-06)Identify anomalous (outliers) system call sequences in security domain (Host based Intrusion Detection System). -
Applying process mining to improve microservices cyber security situational awareness.
Jacob, Stephen; Lee, Brian; Qiao, Yuansong (Athlone Institute of Technology, 2020-06)Cyber Security Incident Response Teams (CSIRTs) for enterprise networks are often overwhelmed by newer, more sophisticated forms of cyber attack. Improved cyber security techniques are in high demand. At present, microservices ... -
An architecture pattern for trusted orchestration in IoT Edge clouds.
Pahl, Claus; El Ioini, Nabil; Helmer, Sven; Lee, Brian (IEEE, 2018-04)Fog and edge architectures provide a link between centralised clouds and the world of IoT and sensors. The architectures consist of devices of different sizes that coordinate the communication with sensors and cloud services, ... -
Bidirectional LSTM autoencoder for sequence based anomaly detection in cyber security.
Chawla, Ashima; Jacob, Paul; Lee, Brian; Fallon, Sheila (United Kingdom Simulation Society, 2019)Cyber-security is concerned with protecting information, a vital asset in today’s world. The volume of data that is generated can be usefully analyzed when cyber-security systems are effectively implemented with the aid ... -
Block-chain empowered multi-robot collaboration to fight COVID-19 and future pandemics
Alsamhi, Saeed H.; Lee, Brian (IEEE, 2021-03-25)This conceptual paper overviews how blockchain technology is involving the operation of multi-robot collaboration for combating COVID-19 and future pandemics. Robots are a promising technology for providing many tasks ... -
Blockchain for decentralized multi-drone to combat COVID-19
Alsamhi, Saeed H.; Lee, Brian; Guizani, Mohsen; Kumar, N.; Qiao, Yuansong; Liu, Xuan (Wiley, 2021-03-17)Currently, drones represent a promising technology for combating Coronavirus disease 2019 (COVID-19) due to the transport of goods, medical supplies to a given target location in the quarantine areas experiencing an epidemic ... -
A container-based edge cloud PaaS architecture based on Raspberry Pi Clusters.
Pahl, Claus; Helmer, Sven; Miori, Lorenzo; Sanin, Julian; Lee, Brian (IEEE, 2016-08)Cloud technology is moving towards multi-cloud environments with the inclusion of various devices. Cloud and IoT integration resulting in so-called edge cloud and fog computing has started. This requires the combination ... -
Containers and clusters for edge cloud architectures - a technology review.
Pahl, Claus; Lee, Brian (IEEE, 2015-10-26)Cloud technology is moving towards more distribution across multi-clouds and the inclusion of various devices, as evident through IoT and network integration in the context of edge cloud and fog computing. Generally, ... -
The context aware security policy language for Zero Trust Network
Xaio, Shiyu; Lee, Brian; Kanwal, Nadia (Athlone Institute of Technology, 2020-06)With the development of the pervasive computing, the number of devices accessing to network is increasing. Though this condition brings us a more convenient and intelligent lifestyle, accompanying with it is the higher ... -
Cooperative industrial multi robot system using multi agent reinforcement learning
Lan, Xi; Lee, Brian; Qiao, Yuansong (Athlone Institute of Technology, 2020-06)This poster describes the research definition process for thisearly stage PhD. Our goal is to investigate the feasibility of using multi-agent deep learning (MADRL) as an approach for solving cooperative multi robot system ... -
CS-Man: computation service management for IoT in-network processing.
Wang, Qian; Lee, Brian; Murray, Niall; Qiao, Yuansong (2016)The Internet of Things (IoT) expects to link billions of devices to the Internet, which will produce massive amounts of data. Current approaches move the IoT data out of the network for processing. It results in long delays ... -
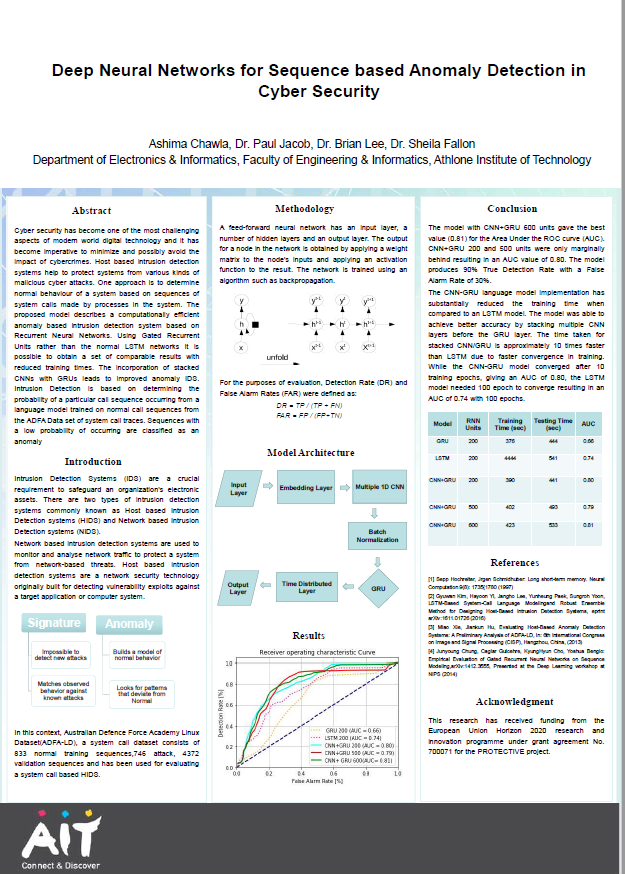
Deep neural networks for sequence based anomaly detection in cyber security
Chawla, Ashima; Jacob, Paul; Lee, Brian; Fallon, Sheila (Athlone Institute of Technology, 2019)Cyber security has become one of the most challenging aspects of modern world digital technology and it has become imperative to minimize and possibly avoid the impact of cybercrimes. Host based intrusion detection systems ... -
Deep reinforcement learning-based industrial robotic manipulation
Imtiaz, Muhammad Babar (Technological University of the Shannon: Midlands Midwest, 2023-09)Pick and place robotic systems can be found in all major industries in order to increase throughput and efficiency. But most of the pick-and-place applications in the industry today have been designed through hard-coded, ... -
Discrete event simulation of a multi robot pick and place system for reinforcement learning research
Lan, Xi; Lee, Brian; Qiao, Yuansong (Technological University of the Shannon Midlands Midwest, 2022-01)This poster described a implementation of simulation environment for a Pick and Place conveyer belt for multi robot system based on the Gym library to be used to train Reinforcement Learning agents - see figure below. ... -
ECE: Exactly-Once-Computation for Collaborative Edge in IoT using Information Centric Networking
Wang, Qian; Lee, Brian; Murray, Niall; Qiao, Yuansong (IEEE, 2023-05-11)—Exactly-once data processing/delivery can be guaranteed in traditional big data processing systems, e.g. Apache Flink. Checkpoint is commonly used as the solution. Each operator in these systems can restart from the ... -
Enhancing cyber attack prevention and detection using application process tracing
Jacob, Stephen (Technological University of the Shannon: Midlands Midwest, 2022-08)Nowadays, software enterprises are being targeted by more advanced cyber-security threat models. Consequently, more sophisticated means of protecting software organisa tions are in high demand. Also, microservices are ... -
Establishing trust in cloud services via integration of cloud trust protocol with a trust label system.
Emeakaroha, Vincent C.; O'Meara, Eoin; Lee, Brian; Lynn, Theo; Morrison, John P. (Springer, 2017-04)Cloud computing has transformed the computing landscape by enabling flexible compute-resource provisioning. The rapid growth of cloud computing and its large-scale nature provide many advantages to business enterprises. ...