Search
Now showing items 21-30 of 31
Applying process mining to improve microservices cyber security situational awareness.
(Athlone Institute of Technology, 2020-06)
Cyber Security Incident Response Teams (CSIRTs) for enterprise networks are often overwhelmed by newer, more sophisticated forms of cyber attack. Improved cyber security techniques are in high demand. At present, microservices ...
A workflow management framework for the dynamic generation of workflows that is independent of the application environment
(IEEE, 2021-06-30)
Workflow is a well-known and widely used technology in business management. Traditional workflow solutions are designed for humans and generally use a graphical representation of workflow elements that reflect the involvement ...
Digital twin: origin to future
(MDPI, 2021-05-24)
Digital Twin (DT) refers to the virtual copy or model of any physical entity (physical twin)
both of which are interconnected via exchange of data in real time. Conceptually, a DT mimics the
state of its physical twin ...
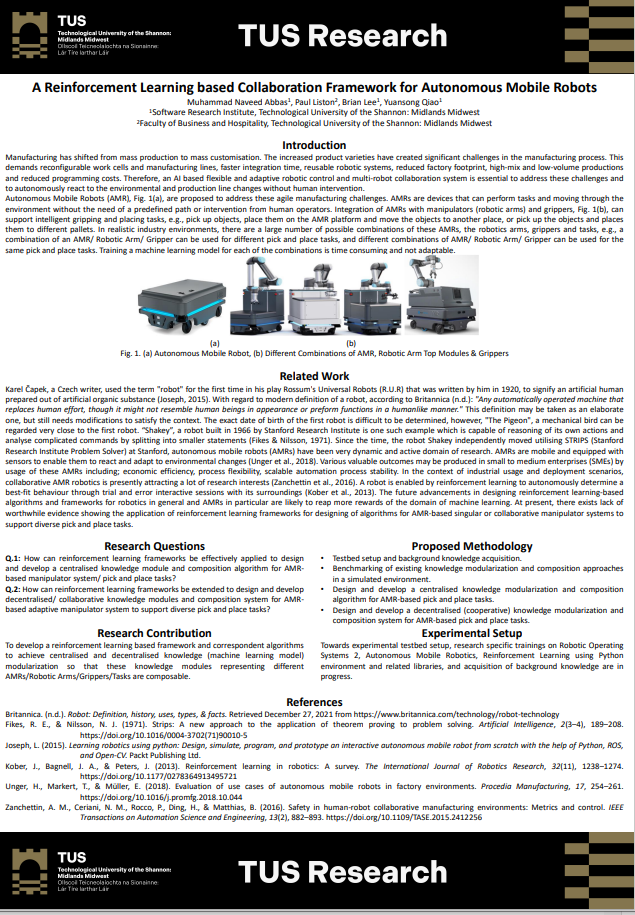
A reinforcement learning based collaboration framework for autonomous mobile robots
(Technological University of the Shannon Midlands Midwest, 2022)
Manufacturing has shifted from mass production to mass customisation. The increased product varieties have created significant challenges in the manufacturing process. This
demands reconfigurable work cells and manufacturing ...
Anomalous distributed traffic: detecting cyber security attacks amongst microservices using graph convolutional networks
(Elsevier, 2022-04-22)
Currently, microservices are trending as the most popular software application design architecture. Software organisations are also being targeted by more cyber-attacks every day and newer security measures are in high ...
Pixdoor: a pixel-space backdoor attack on deep learning models
(IEEE, 2021-08-23)
Deep learning algorithms outperform the machine
learning techniques in various fields and are widely deployed
for recognition and classification tasks. However, recent research
focuses on exploring these deep learning ...
Invisible encoded backdoor attack on DNNs using conditional GAN
(IEEE, 2023-02-17)
Deep Learning (DL) models deliver superior performance and have achieved remarkable results for classification and vision tasks. However, recent research focuses on exploring these Deep Neural Networks (DNNs) weaknesses ...
Prehensile and non-prehensile robotic pick-and-place of objects in clutter using deep reinforcement learning
(MDPI, 2023-01-29)
In this study, we develop a framework for an intelligent and self-supervised industrial
pick-and-place operation for cluttered environments. Our target is to have the agent learn to perform
prehensile and non-prehensile ...
Privacy preserved video summarization of road traffic events for IoT smart cities
(MDPI, 2023-02-09)
The purpose of smart surveillance systems for automatic detection of road traffic accidents
is to quickly respond to minimize human and financial losses in smart cities. However, along with
the self-evident benefits of ...
ECE: Exactly-Once-Computation for Collaborative Edge in IoT using Information Centric Networking
(IEEE, 2023-05-11)
—Exactly-once data processing/delivery can be
guaranteed in traditional big data processing systems, e.g.
Apache Flink. Checkpoint is commonly used as the solution.
Each operator in these systems can restart from the ...