Search
Now showing items 11-20 of 37
Machine learning for smart environments in B5G networks: connectivity and QoS
(Hindawi, 2021-09-20)
The number of Internet of Things (IoT) devices to be connected via the Internet is overgrowing. The heterogeneity and complexity of the IoT in terms of dynamism and uncertainty complicate this landscape dramatically and ...
The context aware security policy language for Zero Trust Network
(Athlone Institute of Technology, 2020-06)
With the development of the pervasive computing, the number of devices accessing to network is increasing. Though this condition brings us a more convenient and intelligent lifestyle, accompanying with it is the higher ...
Shallow and deep learning approaches for network intrusion alert prediction.
(Elsevier, 2020)
The ever-increasing frequency and intensity of intrusion attacks on computer networks worldwide has necessitated intense research efforts towards the design of attack detection and prediction mechanisms. While there are a ...
Property based attestation for a secure cloud monitoring system.
(IEEE, 2014-02)
—In this paper, we consider the problem of trust in
cloud monitoring systems. We design and develop a novel
scheme for trust certification using property based attestation
(PBA). The PBA is based on a trusted platform ...
Implementation of reinforcement learning algorithms for robotic pick and place with non-visual sensing
(TUS Midlands Midwest, 2022)
The term ‘Industry 4.0’ appeared for the first time in 2011 and saw the
introduction of many cutting-edge technologies such as Cyber-Physical
Systems (CPS), Internet of Things (IoT), and Digital Twins (DT). World
leading ...
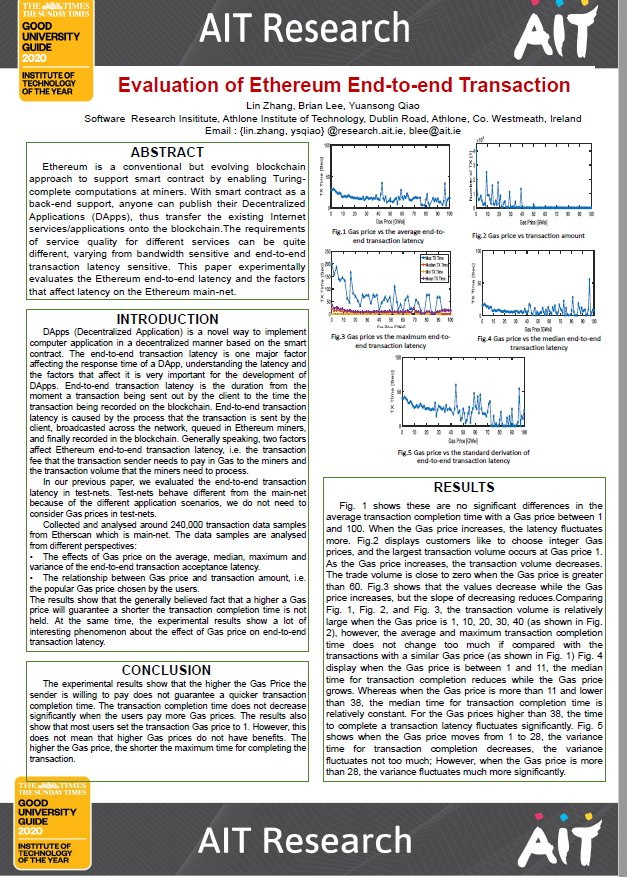
Evaluation of ethereum end-to-end transaction
(Athlone Institute of Technology, 2020-06)
Ethereum is a conventional but evolving blockchain
approach to support smart contract by enabling Turingcomplete
computations at miners. With smart contract as a
back-end support, anyone can publish their Decentralize ...
Green internet of things using UAVs in B5G networks: a review of applications and strategies
(Elsevier, 2021-04-03)
Recently, Unmanned Aerial Vehicles (UAVs) present a promising advanced technology that can enhance people life quality and smartness of cities dramatically and increase overall economic efficiency. UAVs have attained a ...
IProIoT: an in-network processing framework for IoT using information centric networking
(IEEE, 2017-07-27)
The Internet of Things (IoT) network supports various network applications through billions of heterogeneous connected devices. Efficient processing of enormous amounts of IoT data collected and exchanged by these devices ...
Containers and clusters for edge cloud architectures - a technology review.
(IEEE, 2015-10-26)
Cloud technology is moving towards more distribution across multi-clouds and the inclusion of various devices, as evident through IoT and network integration in the context of edge cloud and fog computing. Generally, ...
Bidirectional LSTM autoencoder for sequence based anomaly detection in cyber security.
(United Kingdom Simulation Society, 2019)
Cyber-security is concerned with protecting information, a vital asset in today’s world. The volume of data that is
generated can be usefully analyzed when cyber-security systems are effectively implemented with the aid ...