Browsing Technological University of the Shannon: Midlands Midwest by Author "Fallon, Sheila"
Now showing items 1-14 of 14
-
An analysis of alterations to the SCTP RTO calculation mechanism for WLAN environments
Fallon, Sheila; Jacob, Paul; Qiao, Yuansong; Murphy, Liam; Fallon, Enda; Hanley, Austin (Springer, 2008-01)As a connection oriented transport layer protocol the Stream Control Transmission Protocol (SCTP) inherits many of the features of the Transmission Control Protocol (TCP) including the mechanism by which Retransmission ... -
Anomaly detection in cyber security
Chawla, Ashima; Jacob, Paul; Lee, Brian; Fallon, Sheila (Athlone Institute of Technology, 2020-06)Identify anomalous (outliers) system call sequences in security domain (Host based Intrusion Detection System). -
Architectural design and evaluation for distribution and governance of vehicular information in smart cities
Young, Roger (Athlone Institute of Technology, 2020-07)The rate at which we generate data nowadays has instigated a migration of data processing concepts and technologies from the Cloud-Computing paradigm. The potential destructive impact of “Internet of Things” on the current ... -
An architecture for intelligent data processing on IoT edge devices.
Young, Roger; Fallon, Sheila; Jacob, Paul (IEEE, 2018-05-17)As the Internet of Things edges closer to mainstream adoption, with it comes an exponential rise in data transmission across the current Internet architecture. Capturing and analyzing this data will lead to a wealth ... -
Bidirectional LSTM autoencoder for sequence based anomaly detection in cyber security.
Chawla, Ashima; Jacob, Paul; Lee, Brian; Fallon, Sheila (United Kingdom Simulation Society, 2019)Cyber-security is concerned with protecting information, a vital asset in today’s world. The volume of data that is generated can be usefully analyzed when cyber-security systems are effectively implemented with the aid ... -
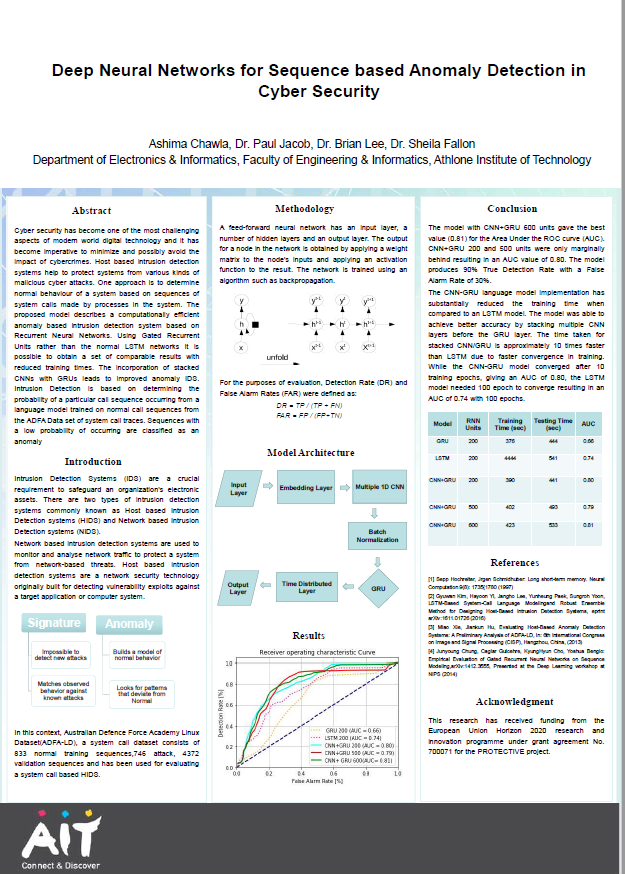
Deep neural networks for sequence based anomaly detection in cyber security
Chawla, Ashima; Jacob, Paul; Lee, Brian; Fallon, Sheila (Athlone Institute of Technology, 2019)Cyber security has become one of the most challenging aspects of modern world digital technology and it has become imperative to minimize and possibly avoid the impact of cybercrimes. Host based intrusion detection systems ... -
Dynamic collaboration of centralized & Edge processing for coordinated data management in an IoT paradigm.
Young, Roger; Fallon, Sheila; Jacob, Paul (IEEE, 2018-05)Over the past decade, much focus in the area of Technology has deviated towards two relatively new areas; "The Internet of Things" and "Machine Learning". Although completely separate technologies, they have one major ... -
A flow based architecture for efficient distribution of vehicular information in smart cities
Young, Roger; Fallon, Sheila; Jacob, Paul (IEEE, 2019-10-22)The Introduction of the Internet of Things has made the vision of “Smart Cities” a very reachable goal. Aggregating data from a wealth of sensors throughout a city, with the aim of improving quality of life for its ... -
A flow based architecture for efficient distribution of vehicular information in smart cities.
Young, Roger; Fallon, Sheila; Jacob, Paul; O'Dwyer, Denis (IEEE, 2019-12-23)The Introduction of the Internet of Things has made the vision of “Smart Cities” a very reachable goal. Aggregating data from a wealth of sensors throughout a city, with the aim of improving quality of life for its ... -
A governance architecture for self-adaption & control in IoT applications.
Young, Roger; Fallon, Sheila; Jacob, Paul (IEEE, 2018-06-25)The “Internet of Things” has become a reality with projections of 28 billion connected devices by 2021. Much R&D is currently focused on creating methods to efficiently handle an influx of data. Flow based programming, ... -
Host based intrusion detection system with combined CNN/RNN model.
Chawla, Ashima; Lee, Brian; Fallon, Sheila; Jacob, Paul (Springer, 2018-09)Cyber security has become one of the most challenging aspects of modern world digital technology and it has become imperative to minimize and possibly avoid the impact of cybercrimes. Host based intrusion detection systems ... -
Host based intrusion detection system with combined CNN/RNN model.
Chawla, Ashima; Lee, Brian; Fallon, Sheila; Jacob, Paul (Springer International Publishing, 2018)Cyber security has become one of the most challenging as- pects of modern world digital technology and it has become imperative to minimize and possibly avoid the impact of cybercrimes. Host based intrusion detection ... -
Intelligent monitoring of IoT devices using neural networks
Chawla, Ashima; Babu, Pradeep; Gawande, Trushnesh; Aumayr, Erik; Jacob, Paul; Fallon, Sheila (IEEE, 2021-03-29)The Internet of Things (IoT) has seen expeditious growth in recent times with 7 billion connected devices in 2020, thus leading to the vital importance of real-time monitoring of IoT devices. Through this paper, we demonstrate ... -
Interpretability and performance of deep neural network based anomaly detection in cyber security and telecommunications
Chawla, Ashima (Technological University of the Shannon: Midlands Midwest, 2022-06)The rapid development of technology and proliferation of data have driven businesses to pursue anomaly detection research. The application of artificial neural networks (ANNs) in anomaly detection achieves the state-of-the-art, ...