Search
Now showing items 1-7 of 7
Access control policy enforcement for zero-trust-networking.
(IEEE, 2018-06)
The evolution of the enterprise computing landscape towards emerging trends such as fog/edge computing and the Industrial Internet of Things (IIoT) are leading to a change of approach to securing computer networks to deal ...
Situational awareness based risk-adaptable access control in enterprise networks.
(Association for Computing Machinery, 2017-03)
As the computing landscape evolves towards distributed architectures such as Internet of Things (IoT),
enterprises are moving away from traditional perimeter based security models toward so called “zero trust
networking” ...
Anomaly detection in cyber security
(Athlone Institute of Technology, 2020-06)
Identify anomalous (outliers) system call sequences in security domain (Host based Intrusion Detection System).
Bidirectional LSTM autoencoder for sequence based anomaly detection in cyber security.
(United Kingdom Simulation Society, 2019)
Cyber-security is concerned with protecting information, a vital asset in today’s world. The volume of data that is
generated can be usefully analyzed when cyber-security systems are effectively implemented with the aid ...
Host based intrusion detection system with combined CNN/RNN model.
(Springer, 2018-09)
Cyber security has become one of the most challenging aspects of modern world digital technology and it has become imperative to minimize and possibly avoid the impact of cybercrimes. Host based intrusion detection systems ...
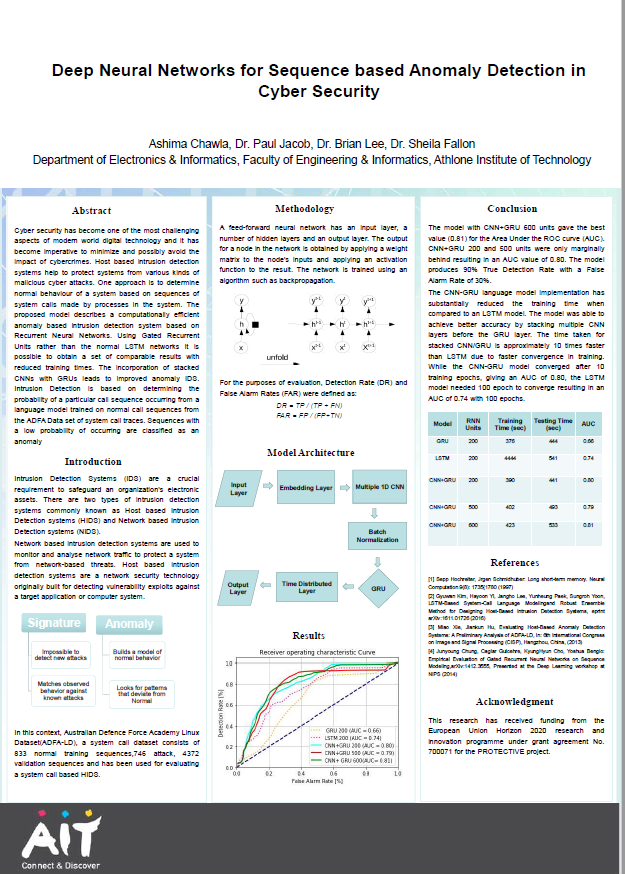
Deep neural networks for sequence based anomaly detection in cyber security
(Athlone Institute of Technology, 2019)
Cyber security has become one of the most challenging
aspects of modern world digital technology and it has
become imperative to minimize and possibly avoid the
impact of cybercrimes. Host based intrusion detection
systems ...
Host based intrusion detection system with combined CNN/RNN model.
(Springer International Publishing, 2018)
Cyber security has become one of the most challenging as-
pects of modern world digital technology and it has become imperative
to minimize and possibly avoid the impact of cybercrimes. Host based
intrusion detection ...