Search
Now showing items 1-2 of 2
Towards improved trust in threat intelligence sharing using Blockchain and trusted computing.
(IEEE Xplore, 2019-10)
Threat intelligence sharing is posited as an important aid to help counter cybersecurity attacks and a number of threat intelligence sharing communities exist. There is a general consensus that many challenges remain to ...
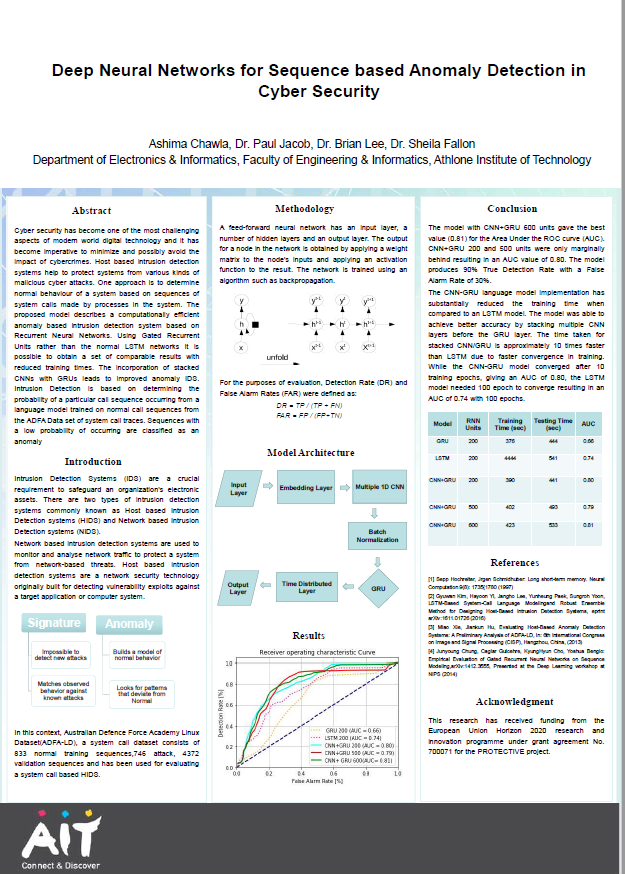
Deep neural networks for sequence based anomaly detection in cyber security
(Athlone Institute of Technology, 2019)
Cyber security has become one of the most challenging
aspects of modern world digital technology and it has
become imperative to minimize and possibly avoid the
impact of cybercrimes. Host based intrusion detection
systems ...