Search
Now showing items 21-30 of 63
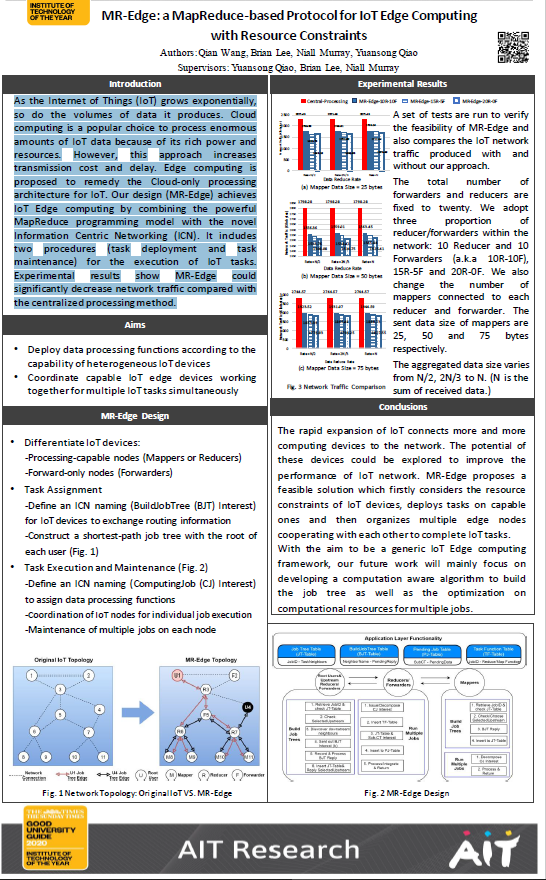
MR-Edge: a MapReduce-based protocol for IoT Edge computing
(Athlone Institute of Technology, 2020-06)
As
the Internet of Things ( grows exponentially,
so do the volumes of data it produces Cloud
computing is a popular choice to process enormous
amounts of IoT data because of its rich power and
resources However, this ...
Towards improved trust in threat intelligence sharing using Blockchain and trusted computing.
(IEEE Xplore, 2019-10)
Threat intelligence sharing is posited as an important aid to help counter cybersecurity attacks and a number of threat intelligence sharing communities exist. There is a general consensus that many challenges remain to ...
A QoE Evaluation of an Augmented Reality Procedure Assistance Application
(2020-05)
Augmented reality (AR) is a key technology to enhance worker effectiveness during increasing automation of repetitive jobs in the workplace. AR will achieve this by assisting the user to successfully perform complex and ...
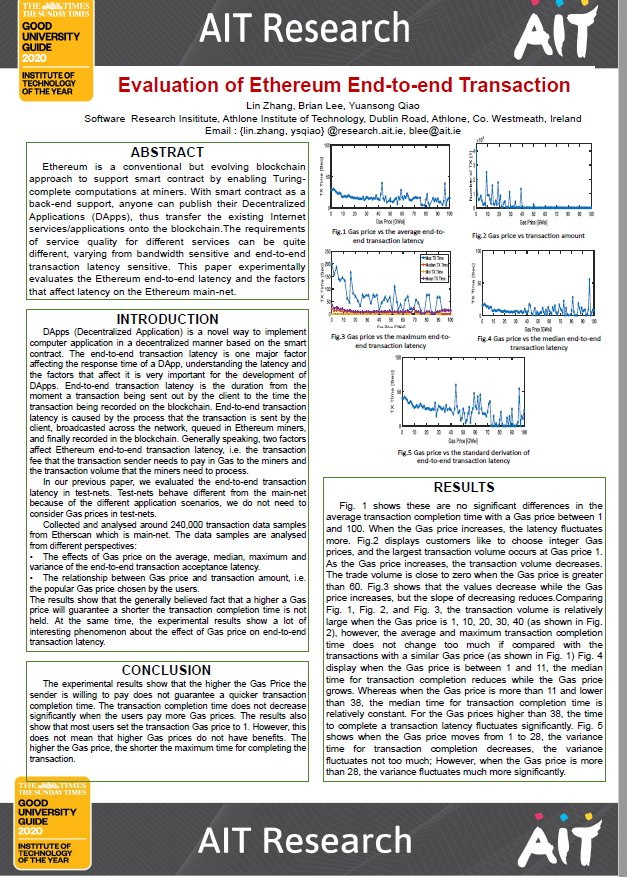
Evaluation of ethereum end-to-end transaction
(Athlone Institute of Technology, 2020-06)
Ethereum is a conventional but evolving blockchain
approach to support smart contract by enabling Turingcomplete
computations at miners. With smart contract as a
back-end support, anyone can publish their Decentralize ...
Green internet of things using UAVs in B5G networks: a review of applications and strategies
(Elsevier, 2021-04-03)
Recently, Unmanned Aerial Vehicles (UAVs) present a promising advanced technology that can enhance people life quality and smartness of cities dramatically and increase overall economic efficiency. UAVs have attained a ...
IProIoT: an in-network processing framework for IoT using information centric networking
(IEEE, 2017-07-27)
The Internet of Things (IoT) network supports various network applications through billions of heterogeneous connected devices. Efficient processing of enormous amounts of IoT data collected and exchanged by these devices ...
Anomaly detection in cyber security
(Athlone Institute of Technology, 2020-06)
Identify anomalous (outliers) system call sequences in security domain (Host based Intrusion Detection System).
MCP2P: Layer-dependency-aware live MVC video streaming over peer-to-peer networks.
(Elsevier, 2018-07)
Multiview video supports observing a scene from different viewpoints. The Joint Video Team (JVT) developed H.264/MVC to enhance the compression efficiency for multiview video, however, MVC encoded multiview video (MVC ...
Containers and clusters for edge cloud architectures - a technology review.
(IEEE, 2015-10-26)
Cloud technology is moving towards more distribution across multi-clouds and the inclusion of various devices, as evident through IoT and network integration in the context of edge cloud and fog computing. Generally, ...
Bidirectional LSTM autoencoder for sequence based anomaly detection in cyber security.
(United Kingdom Simulation Society, 2019)
Cyber-security is concerned with protecting information, a vital asset in today’s world. The volume of data that is
generated can be usefully analyzed when cyber-security systems are effectively implemented with the aid ...