Search
Now showing items 1-6 of 6
Towards improved trust in threat intelligence sharing using Blockchain and trusted computing.
(IEEE Xplore, 2019-10)
Threat intelligence sharing is posited as an important aid to help counter cybersecurity attacks and a number of threat intelligence sharing communities exist. There is a general consensus that many challenges remain to ...
Bidirectional LSTM autoencoder for sequence based anomaly detection in cyber security.
(United Kingdom Simulation Society, 2019)
Cyber-security is concerned with protecting information, a vital asset in today’s world. The volume of data that is
generated can be usefully analyzed when cyber-security systems are effectively implemented with the aid ...
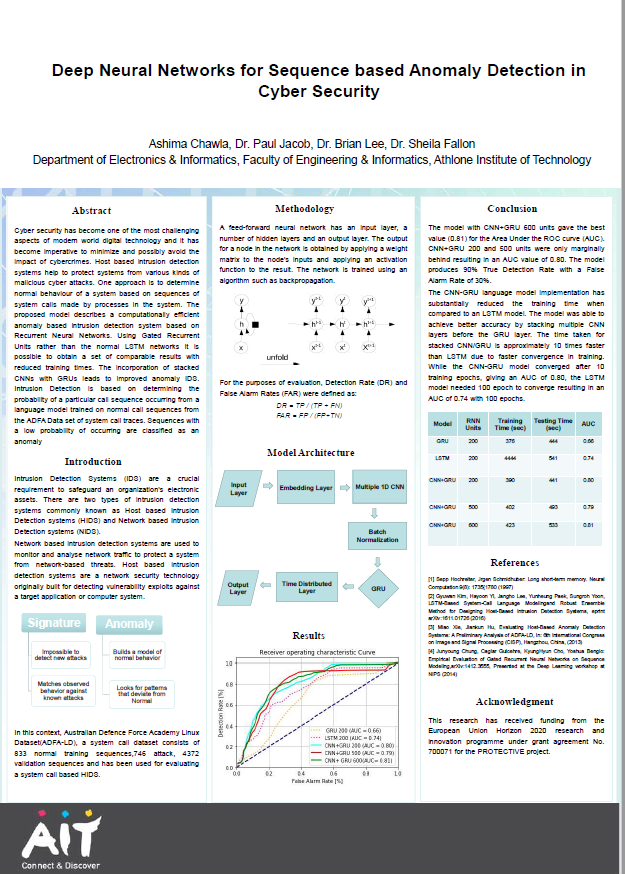
Deep neural networks for sequence based anomaly detection in cyber security
(Athlone Institute of Technology, 2019)
Cyber security has become one of the most challenging
aspects of modern world digital technology and it has
become imperative to minimize and possibly avoid the
impact of cybercrimes. Host based intrusion detection
systems ...
MR-Edge: a MapReduce-based Protocol for IoT Edge Computing with resource constraints.
(IEEE Xplore, 2019)
Edge computing is proposed to remedy the
Cloud-only processing architecture for Internet of Things (IoT)
because of the massive amounts of IoT data. The challenge is
how to deploy and execute data processing tasks ...
A quality of experience evaluation comparing augmented reality and paper based instruction for complex task assistance.
(IEEEXplore, 2019-11-18)
Augmented reality (AR) can support a user in
performing an expert task by overlaying real world objects with
the domain specific information required to complete the task.
Understanding how users can process and use ...
Visual surveillance within the EU general data protection regulation: a technology perspective.
(IEEE, 2019-08-23)
From an individual's perspective, technological advancement has merits and demerits. Video captured by surveillance cameras while a person goes about their daily life may improve their personal safety but the images collected ...