Search
Now showing items 1-7 of 7
Hop-by-hop congrestion measurement and practical active queue management in NDN
(IEEE, 2020-12)
Content replication and name-based routing in Named Data Network (NDN) naturally lead to connectionless multi-source and multipath transmissions. Traditional congestion control designed for end-to-end connections cannot ...
Preserving chain-of-evidence in surveillance videos for authentication and trust-enabled sharing
(IEEE, 2020)
Surveillance video recording is a powerful method of deterring unlawful activities. A robust data protection-by-design solution can be helpful in terms of making a captured video immutable, as such recordings cannot become ...
Cooperative industrial multi robot system using multi agent reinforcement learning
(Athlone Institute of Technology, 2020-06)
This poster describes the research definition process for thisearly stage PhD.
Our goal is to investigate the feasibility of using multi-agent deep learning (MADRL) as an approach for solving cooperative multi robot system ...
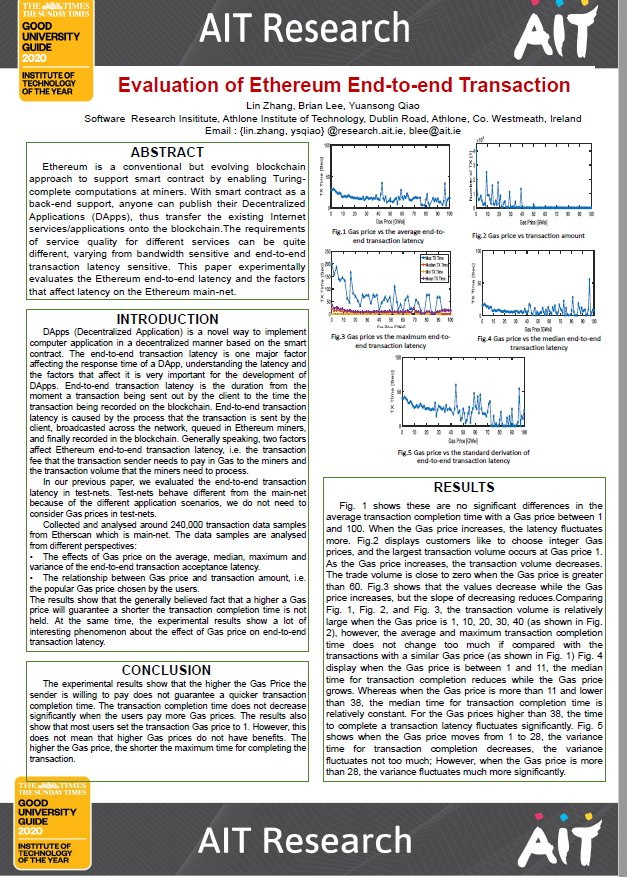
Evaluation of ethereum end-to-end transaction
(Athlone Institute of Technology, 2020-06)
Ethereum is a conventional but evolving blockchain
approach to support smart contract by enabling Turingcomplete
computations at miners. With smart contract as a
back-end support, anyone can publish their Decentralize ...
Smart contract driven resource management for edge computing
(Athlone Institute of Technology, 2020-06)
Edge computing has witnessed a rapid growth in the past few years
as more and more and resources are getting connected to the
Internet. The Internet is not gaining any benefits from the current
implementation of ad hoc ...
MuLViS: multi-level encryption based security system for surveillance videos
(IEEE, 2020-09-18)
Video Surveillance (VS) systems are commonly deployed for real-time abnormal event detection and autonomous video analytics. Video captured by surveillance cameras in real-time often contains identifiable personal information, ...
Applying process mining to improve microservices cyber security situational awareness.
(Athlone Institute of Technology, 2020-06)
Cyber Security Incident Response Teams (CSIRTs) for enterprise networks are often overwhelmed by newer, more sophisticated forms of cyber attack. Improved cyber security techniques are in high demand. At present, microservices ...