Search
Now showing items 1-4 of 4
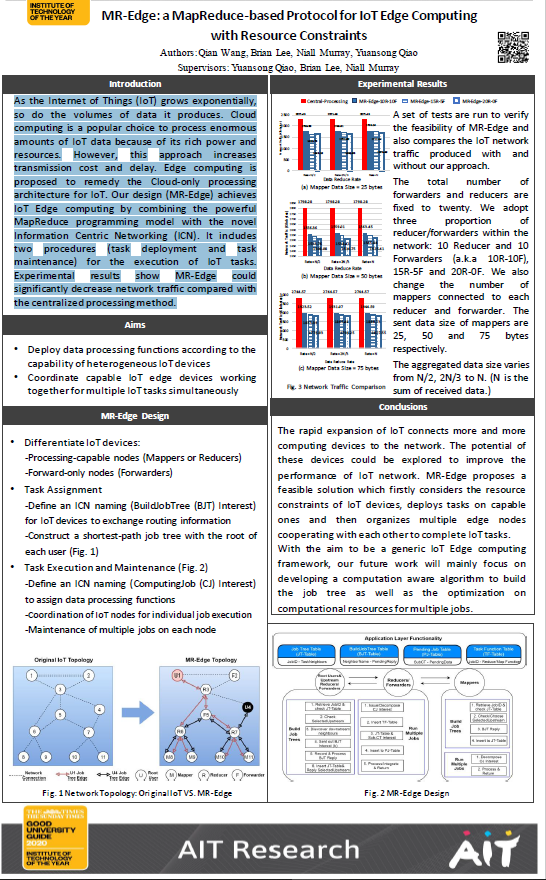
MR-Edge: a MapReduce-based protocol for IoT Edge computing
(Athlone Institute of Technology, 2020-06)
As
the Internet of Things ( grows exponentially,
so do the volumes of data it produces Cloud
computing is a popular choice to process enormous
amounts of IoT data because of its rich power and
resources However, this ...
Anomaly detection in cyber security
(Athlone Institute of Technology, 2020-06)
Identify anomalous (outliers) system call sequences in security domain (Host based Intrusion Detection System).
Applying process mining to improve microservices cyber security situational awareness.
(Athlone Institute of Technology, 2020-06)
Cyber Security Incident Response Teams (CSIRTs) for enterprise networks are often overwhelmed by newer, more sophisticated forms of cyber attack. Improved cyber security techniques are in high demand. At present, microservices ...
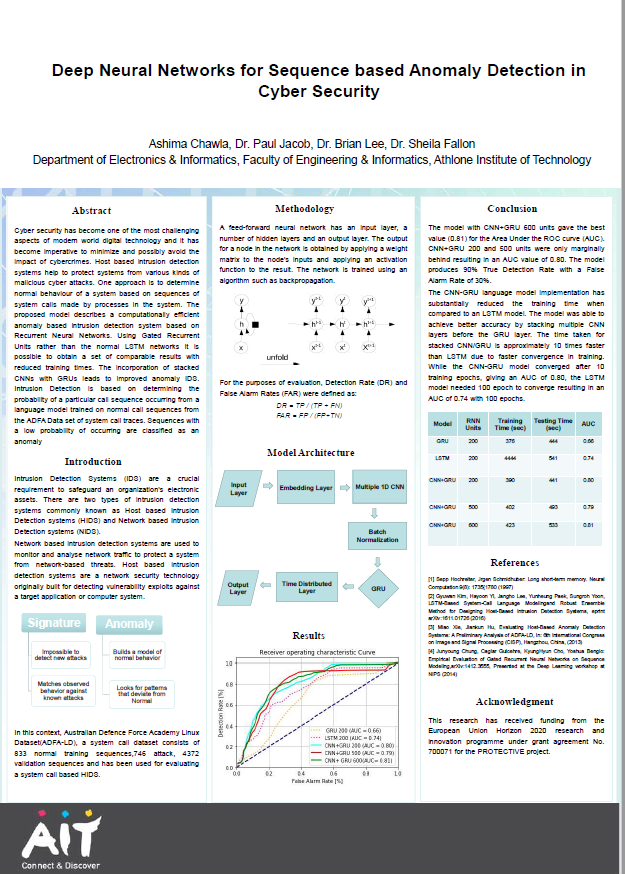
Deep neural networks for sequence based anomaly detection in cyber security
(Athlone Institute of Technology, 2019)
Cyber security has become one of the most challenging
aspects of modern world digital technology and it has
become imperative to minimize and possibly avoid the
impact of cybercrimes. Host based intrusion detection
systems ...