Search
Now showing items 1-10 of 11
A survey of modern deep learning based object detection models
(Elsevier, 2022-06-30)
Object Detection is the task of classification and localization of objects in an image or video. It has gained prominence in recent years due to its widespread applications. This article surveys recent developments in deep ...
Optimization of Ethereum transaction and block delivery performance
(2022)
Blockchain is a type of distributed ledger. It is a chain of blocks. Each block contains a series of transactions. Each transaction
is for a value transfer or a smart contract execution. The main purpose of the blockchain ...
Optimization of decentralized payment system for future internet
(Technological University of the Shannon Midlands Midwest, 2022)
With the development of Internet,
the future Internet architecture will
have many features. For example,
the high volume of content together
with new emerging and missioncritical applications, that it will
possibly ...
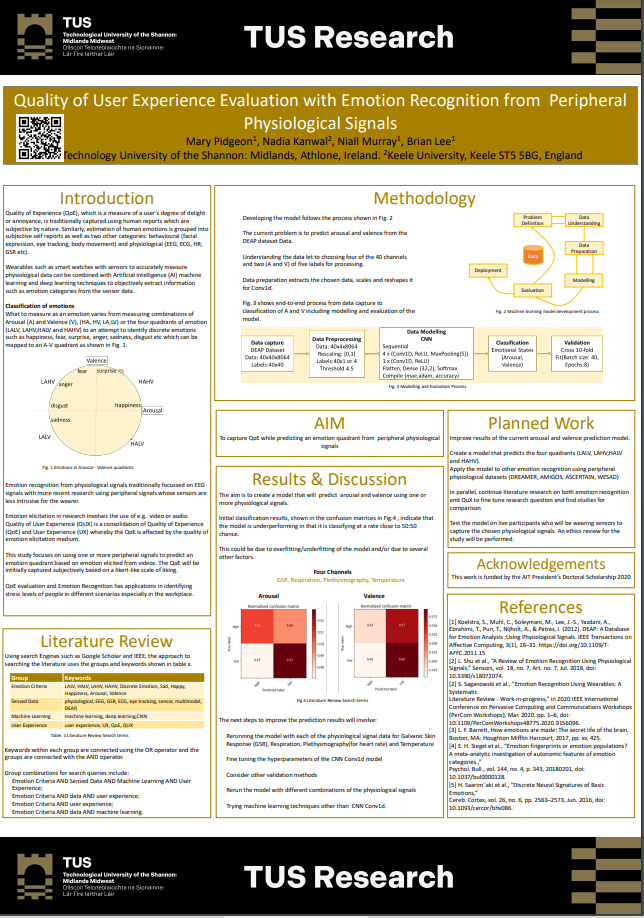
Quality of user experience evaluation with emotion recognition from peripheral physiological signals
(Technological University of the Shannon Midlands Midwest, 2022)
Quality of Experience (QoE), which is a measure of a user’s degree of delight
or annoyance, is traditionally captured using human reports which are
subjective by nature. Similarly, estimation of human emotions is grouped ...
Implementation of reinforcement learning algorithms for robotic pick and place with non-visual sensing
(TUS Midlands Midwest, 2022)
The term ‘Industry 4.0’ appeared for the first time in 2011 and saw the
introduction of many cutting-edge technologies such as Cyber-Physical
Systems (CPS), Internet of Things (IoT), and Digital Twins (DT). World
leading ...
Discrete event simulation of a multi robot pick and place system for reinforcement learning research
(Technological University of the Shannon Midlands Midwest, 2022-01)
This poster described a implementation of simulation environment for a Pick and
Place conveyer belt for multi robot system based on the Gym library to be used to
train Reinforcement Learning agents - see figure below. ...
SoK: context and risk aware access control for zero trust systems
(Wiley/Hindawi, 2022-06-30)
Evolving computing technologies such as cloud, edge computing, and the Internet of )ings (IoT) are creating a more complex,
dispersed, and dynamic enterprise operational environment. New security enterprise architectures ...
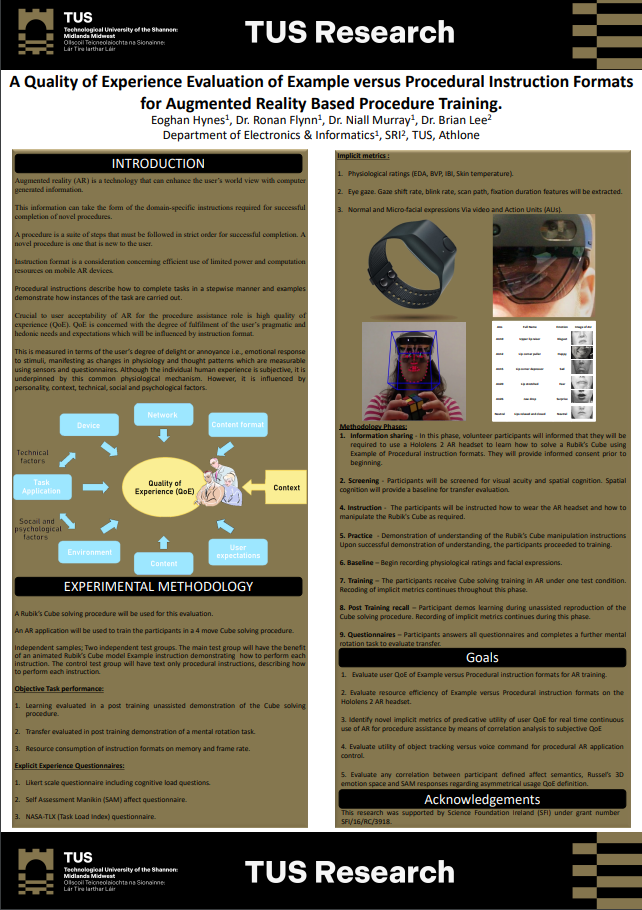
A quality of experience evaluation of example versus procedural instruction formats for augmented reality based procedure training
(TUS Midlands Midwest, 2022)
Augmented reality (AR) is a technology that can enhance the user’s world view with computer
generated information.
This information can take the form of the domain-specific instructions required for successful
completion ...
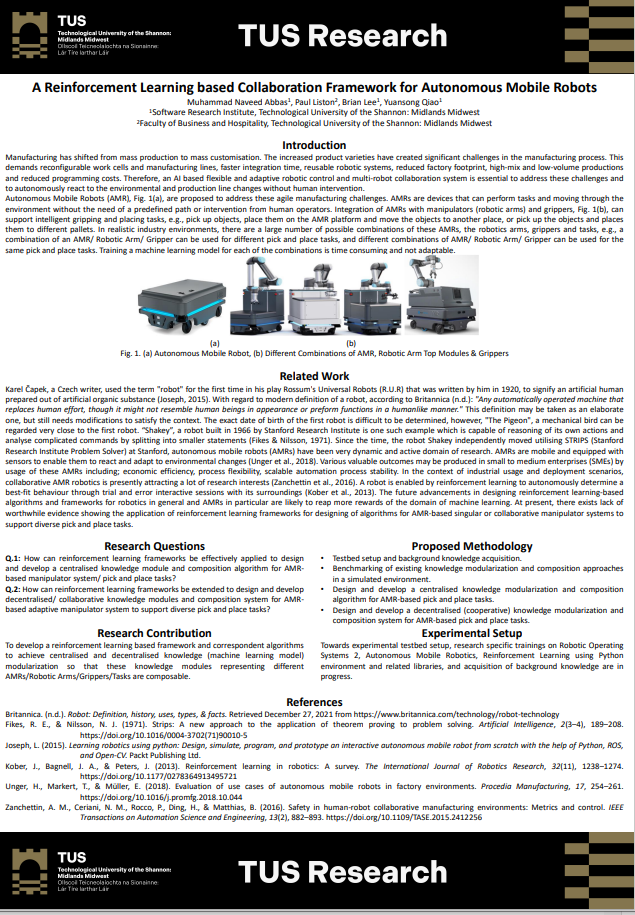
A reinforcement learning based collaboration framework for autonomous mobile robots
(Technological University of the Shannon Midlands Midwest, 2022)
Manufacturing has shifted from mass production to mass customisation. The increased product varieties have created significant challenges in the manufacturing process. This
demands reconfigurable work cells and manufacturing ...
Anomalous distributed traffic: detecting cyber security attacks amongst microservices using graph convolutional networks
(Elsevier, 2022-04-22)
Currently, microservices are trending as the most popular software application design architecture. Software organisations are also being targeted by more cyber-attacks every day and newer security measures are in high ...